As of August 18, 2014, all Boot Loaders and ScreenOS Firmwares downloaded from the Juniper Networks
Software Download Site are signed with the New Image Authentication Certificate.ScreenOS includes the ability to determine the authenticity of binary images provided by Juniper Networks. An image (also known as “firmware”) authentication signature has been incorporated into each ScreenOS build since version 2.6.1r1. When the ScreenOS authentication certificate (also known as “image key” or “imagekey.cer”) has been loaded beforehand onto a Juniper Networks firewall or VPN device (ISG Series, NetScreen Series, and SSG Series), each time the device is rebooted, ScreenOS will validate the authenticity of the image saved in flash. If the validation fails, the device will not load the image. The same logic is applied to ScreenOS firmware upgrade/downgrade. If the image cannot be validated by the installed image key, the upgrade/downgrade will fail.Validating the authenticity of an image enhances security and stability. When this feature is enabled, ScreenOS rejects illegitimate or damaged images before they will be booted onto the device, forcing the system administrator to save an authentic software image in the device before it will boot, and thereby protecting the device against unsafe and potentially unstable software.
SOLUTION:
Validating the Image Authentication Certificate
It is important to ensure the integrity of the image key itself before you load it on the Juniper Networks security device. You can confirm the image key’s integrity by comparing the checksum of the imagekey.cer certificate file to the value below. A tool such as md5sum, sha1sum, andsha256sum for Unix/Linux can be used.
$ md5sum imagekey.cer
99def4b80b75ed65aad52a5fc3ed1131 imagekey.cer
$ sha1sum imagekey.cer
06c3c15b88de548b18814d4389d18a20f65a5845 imagekey.cer
$ sha256sum imagekey.cer
02b107f0679bc5d5aa0ab49be52043bb31f2a010a980573c53dc3fc815e1d7f3 imagekey.cer
$ md5sum imagekey.cer
ccfcd027e20c9cc38b5d8dac17c7199f imagekey.cer
$ sha1sum imagekey.cer
2af0d97abbb58821650445cd517050fd0cfa2684 imagekey.cer
$ sha256sum imagekey.cer
bab2f722cbba13a73d9af4c17af9c34d62ac71b4c9e8bbb9bac5df1fdceb0261 imagekey.cer
Validating the Boot Loader and the ScreenOS Firmware
There are no code or contents changes on the newly released boot loaders and ScreenOS firmwares, these files are signed with the new image key only. Therefore, the version numbers are same as before.
In order to distinguish whether the device is running with old ScreenOS firmware that is signed with the old image key, you can check the non-zero values of the image key using hidden CLI exec pki test skey command. Refer to 2. Checking the Installed Image Key. Also you can refer to KB29296 – ScreenOS and Boot Loader Checksum Values Signed by Old and New Image Key.
Finally when you feel confident about the integrity of the new image key and know that the currently running ScreenOS firmware is signed by the old image key, you can follow the below steps to install the new image key, and boot loader/ScreenOS firmware that are signed with the new image key.
1. Saving the Configuration
Before you proceed the following steps, please make sure to backup the configuration, you can do it through either the WebUI and the CLI.
On the WebUI, navigate to Configuration > Update > Config File > click “Save to File”
On the CLI, type save config to tftp <IP address of TFTP server> <config filename>
For example,
SSG550-> save config to tftp 172.22.152.251 ssg550_config_backup
Read the current config.
Save configurations (3064 bytes) to ssg550_config_backup on TFTP server 172.22.152.251.
!!!!!!!!!!!!!!
tftp transferred records = 6
tftp success!
TFTP Succeeded
2. Checking the Installed Image Key
If an image key is already installed, you will see output similar to the below (non-zero values). If the output shows all zero (0), then there is no installed image key.
NOTE: The device cannot store more than one image key. When you install the new image key, it overwrites the previous key. The installation status of the image key can be checked through hidden CLI exec pki test skey command only.
SSG550-> exec pki test skey
(snip)
KEY1 N/A len =432
308201ac02010002818100fd7f53811d75122952df4a9c2eece4e7f611b7523cef4400c31e3f80b651 magic1 = f7e9294b magic2=0
KEY2 N/A len =432
308201ac02010002818100fd7f53811d75122952df4a9c2eece4e7f611b7523cef4400c31e3f80b651 magic1 = f7e9294b magic2=0
KEY3 N/A len =432
308201ac02010002818100fd7f53811d75122952df4a9c2eece4e7f611b7523cef4400c31e3f80b651 magic1 = f7e9294b magic2=0
NOTE: The above non-zero values are indicating the old image key (308201ac ….). If you wish to update the image key to the new key, then go to next step 3. Updating the Image Key. The new image key’s values are starting with (308201ad ….) from left to right direction. If the new image key is installed already, then go to step 4. Upgrading ScreenOS.
The following example shows that an image key is not installed (all zero values).
SSG550-> exec pki test skey
(snip)
KEY1 N/A len =0
0000000000000000000000000000000000000000000000000000000000000000000000000000000000 magic1 = f7e9294b magic2=dead1234
KEY2 N/A len =0
0000000000000000000000000000000000000000000000000000000000000000000000000000000000 magic1 = f7e9294b magic2=dead1234
KEY3 N/A len =0
0000000000000000000000000000000000000000000000000000000000000000000000000000000000 magic1 = f7e9294b magic2=dead1234
NOTE: If no image key is installed and you do not want to authenticate the boot loader (for ISG Series and NetScreen Series only) and ScreenOS in future, skip Step 3. Updating the Image Key.
3. Updating the Image Key
If a WebUI access or a TFTP server is available, you can install the new image key through the WebUI or the CLI.
On the WebUI :
- Download the new image key (imagekey.cer)
- Save it to accessible local storage
- Login to the device.
- Navigate to ”Configuration > Update > ScreenOS/Keys” using the navigation tree on the left side of the screen
- Select the ”Image Signature Key Update” radio button and click Browse
- Navigate to the location where you saved the image key and click Open
- Click Apply
On the CLI :
- Download the new image key (imagekey.cer)
- Save it to TFTP server
- Make a console, Telnet, or SSH connection to the Juniper Networks security device
- Login to the device
- Type save image-key tftp (IP address of tftp server) imagekey.cer command
For example,
SSG550-> save image-key tftp 172.22.152.251 new/imagekey.cer
Load file from TFTP 172.22.152.251 (file: new/imagekey.cer).
!!!!!
tftp received octets = 863
tftp success!
Done
TFTP Succeeded
If the image key is installed successfully, you will see output similar to the below (non-zero values). If the output shows all zero (0), then the image key is not installed.
SSG550-> exec pki test skey
(snip)
KEY1 N/A len =433
308201ad02010002818100fd7f53811d75122952df4a9c2eece4e7f611b7523cef4400c31e3f80b651 magic1 = f7e9294b magic2=0
KEY2 N/A len =433
308201ad02010002818100fd7f53811d75122952df4a9c2eece4e7f611b7523cef4400c31e3f80b651 magic1 = f7e9294b magic2=0
KEY3 N/A len =433
308201ad02010002818100fd7f53811d75122952df4a9c2eece4e7f611b7523cef4400c31e3f80b651 magic1 = f7e9294b magic2=0
If only a CLI access is available without TFTP server, you cannot install the new image key, then delete the installed old image key using CLI delete crypto auth-key command and go to next step 4. Upgrading ScreenOS.
The following example shows that no image key is available after deleting the image key.
SSG550-> delete crypto auth-key
SSG550-> exec pki test skey
(snip)
KEY1 N/A len =0
0000000000000000000000000000000000000000000000000000000000000000000000000000000000 magic1 = f7e9294b magic2=0
KEY2 N/A len =0
0000000000000000000000000000000000000000000000000000000000000000000000000000000000 magic1 = f7e9294b magic2=0
KEY3 N/A len =0
0000000000000000000000000000000000000000000000000000000000000000000000000000000000 magic1 = f7e9294b magic2=0
NOTE: Please do not execute CLI delete crypto file command. It will delete all crypto files in the device that might be used for other services.
NOTE: You cannot delete image key through WebUI.
4. Upgrading ScreenOS
On ISG1000/2000, NS5200/NS5400 (boot loader upgrade is required) :
You must have a console connection and a TFTP server that can be reachable through the ‘mgt’ interface because the device will prompt you to install a boot loader if it cannot authenticate the installed boot loader using the new image key.
While the device boots up, it checks the integrity of installed boot loader and ScreenOS firmware.
NOTE: If the old image key is deleted using CLI delete crypto auth-key command, the device skips integrity check of the boot loader and ScreenOS firmware while boots up. You will see Ignore image authentication! message on the console while the device boots up.
On the CLI :
1. Download the ScreenOS firmware signed with the new image key from the
ScreenOS Download site
2. Save it to TFTP server
3. Login to the device through the console port
4. Type
save software from tftp (IP address of TFTP server) (ScreenOS image filename) to flash command
For example,
ns5200-> save software from tftp 172.22.152.251 new/ns5000.6.3.0-M2A.r17.0 to flash
Load software from TFTP 172.22.152.251 (file: new/ns5000.6.3.0-M2A.r17.0).
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
(snip)
tftp received octets = 13541072
tftp success!
TFTP Succeeded
Save to flash. It may take a few minutes ...platform = 15, cpu = 16, version = 18
update new flash image (04243150,13541072)
platform = 15, cpu = 16, version = 18
offset = 20, address = 4000000, size = 13540994
date = 71c0efb8, sw_version = 71c0efbc, cksum = c491f61c
Image authenticated!
Program flash (13541072 bytes) ...
++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++done
Done
5. Reboot the device, type reset command and install the boot loader that is singed with the new image key
NOTE: While the device boots up, it will generate the following messages on the console to guide you to install the boot loader that is signed by the new image key.
OS Loader File Name []: (type boot loader file name)
Self IP Address []: (TFTP client (device) IP address)
TFTP IP Address []: (TFTP server IP address)
For example,
ns5200-> reset
System reset, are you sure? y/[n] y
In reset ...
Juniper Networks NS-5000-II BootROM Version 1.0.0 (Checksum: FE499CCD)
Copyright (c) 1998-2004 Juniper Networks, Inc.
Total physical memory: 2048MB
Test - Pass
Initialization................ Done
Hit key 'X' and 'A' sequentially to update OS Loader....
Loading OS Loader from on-board flash memory... ++++
Done!
********Invalid DSA signature <- The installed boot loader (OS Loader) cannot be authenticated using the new image key
********Bogus image - not authenticated
OS Loader File Name [new/ns5000.6.3.0-M2A.r17.0]: new/Load5000v104.d <- Boot loader file signed with the new image key
Self IP Address [172.19.50.252]: 172.22.152.49
TFTP IP Address [172.19.50.129]: 172.22.152.251
Save loader config (56 bytes)... Done
Loading file "new/Load5000v104.d"...
(snip)
Loaded successfully! (size = 447,576 bytes)
Image authenticated! <- Boot loader is authenticated using the new image key
Program OS Loader to on-board flash memory... ++++
Done!
Start loading...
....................
Done.
Juniper Networks NS-5000-II OS Loader Version 1.0.4
Initialize FBTL 0.. Done
Hit any key to load new firmware
Hit any key to load new firmware
Hit any key to load new firmware
Hit any key to load new firmware
Loading default system image from on-board flash disk...
++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++
Done! (size = 13,631,488 bytes)
Image authenticated! <- ScreenOS firmware is authenticated using the new image key
Start loading...
(snip)
Done.
Configuring Imperial FPGA... Done
Juniper Networks, Inc
NS-5000 System Software
Copyright, 1997-2008
Version 6.3.0r17.0
(snip)
NOTE: After the device boots up successfully, you can check the version of the installed boot loader through the CLI get system command, look for the value of “OS Loader Version”.
ns5200-> get system
Product Name: NetScreen-5200-II
Serial Number: 0040012001000011, Control Number: 00000000
Hardware Version: 3010(0)-(04), FPGA checksum: 00000000, VLAN1 IP (0.0.0.0)
Software Version: 6.3.0r17.0, Type: Firewall+VPN
BOOT ROM Version: 1.0.0
OS Loader Version: 1.0.4
(snip)
On SSG 20/140/320M/350M/520/520M/550/550M :
It is not required to update the current boot loader because the integrity check of the boot loader is only done during the installation of a boot loader. During boot-up of the device there is no integrity check done for the boot loader using the image key. Therefore the existing boot loader on the SSG device will keep working correctly after updating the image key on the device.
NOTE: If the old image key is deleted using CLI delete crypto auth-key command, the device skips the integrity check of the ScreenOS firmware while the device boots up. You will see the Ignore image authentication! message on the console while the device boots up.
On the WebUI :
- Download the ScreenOS firmware signed with the new image key from the ScreenOS Download site
- Save it to accessible local storage.
- Login to the device.
- Navigate to ”Configuration > Update > ScreenOS/Keys” using the navigation tree on the left side of the screen.
- Select the ”Firmware Update (ScreenOS)” radio button and click Browse.
- Navigate to the location where you saved the new image key and click Open.
- Click Apply.
NOTE: If the device has the old image key and you try to install a ScreenOS firmware image that is signed by the new image key, the installation process will stop because the ScreenOS firmware cannot be authenticated using the old image key. You will see a pop-up window displaying “Firmware update failed”. In this case, you need to either install the new image key prior to installing the new ScreenOS firmware or delete the image key (refer to the above step 3. Updating the Image Key).
On the CLI :
1. Download the ScreenOS firmware signed with the new image key from the
ScreenOS Download site
2. Save it to accessible local storage.
3. Login to the device
4. Type
save software from tftp (IP address of TFTP server) (ScreenOS image filename) to flash command
SSG550-> save software from tftp 172.22.152.251 new/ssg500.6.3.0r17.0 to flash
Load software from TFTP 172.22.152.251 (file: new/ssg500.6.3.0r17.0).
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
(snip)
tftp received octets = 11627247
tftp success!
TFTP Succeeded
Save to flash. It may take a few minutes ...platform = 23, cpu = 11, version = 2
update new flash image (02572fd0,11627247)
platform = 23, cpu = 11, version = 2
offset = 20, address = 0, size = 11627169
date = 9422, sw_version = 808031, cksum = 954806c3
Program flash (11627247 bytes) ...
(snip)
5. After successful ScreenOS firmware installation, type reset command to reboot the device
NOTE: If the ScreenOS firmware is not successfully authenticated by the new image key during installation, the error messages “Invalid image!!!” and “Bogus image – not authenticated!!!” will be displayed. When the upgrade went successfully, on the next reboot the device will show ”Image authenticated!”on the console.
SSG550-> reset
System reset, are you sure? y/[n] y
In reset ...
(snip)
ScreenOS Saipanloader V1.0.7
Built Mar 19 2009/15:54:12
watchdog_probe, 1132 bus/dev/fn = 0/248 ich = 2640
boot_drive = 80
start1 = 0768, start2 = 3840
Hit 'X' and 'A' to upgrade bootloadermounting FAT16 partition
file size = 112
size = 112, sizeof(nvram_rec) = 112
Hit any key to load new firmware
Hit any key to load new firmware
Hit any key to load new firmware
Hit any key to load new firmware/$nsboot$.bin
file size = 11627247
hdr->magic_number = 81ba16ee, hdr->platform_type = 1700, hdr->cpu_type = 11
Image authenticated!
(snip)
NOTE: If the device has the old image key and you try to install ScreenOS firmware that is signed with the new image key, the installation process will stop because the ScreenOS firmware cannot be authenticated using the old image key. You will see output similar to the below. In this case, you need to either install the new image key prior to installing the ScreenOS firmware or delete the image key (refer to the above step 3. Updating the Image Key).
SSG550-> save software from tftp 172.22.152.251 new/ssg500.6.3.0r17.0 to flash
Load software from TFTP 172.22.152.251 (file: new/ssg500.6.3.0r17.0).
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
(snip)
tftp received octets = 11627247
tftp success!
TFTP Succeeded
Save to flash. It may take a few minutes ...platform = 23, cpu = 11, version = 2
update new flash image (02572fd0,11627247)
platform = 23, cpu = 11, version = 2
offset = 20, address = 0, size = 11627169
date = 9422, sw_version = 808031, cksum = 954806c3
********Invalid image!!! ********Bogus image - not authenticated!!!
(snip)
NOTE: If you would like to update the boot loader that is signed with the new image key on SSG Series, you must have a console connection and a TFTP server that can be reachable through the pre-assigned interface(s) in the boot loader mode (mostly ‘eth0/0’ interface) and manually interrupt the boot sequence by holding ‘Shift key’ and hit ‘X‘ and ‘A’ sequentially when the “Hit ‘X’ and ‘A’ to upgrade bootloader” message is shown on the console.
After installing the new image key, type CLI reset command to reboot the device. Then keep the ‘Shift key’ down and hit ‘X’ and ‘A’ sequentially.
SSG550-> reset
System reset, are you sure? y/[n] y
In reset ...
(snip)
ScreenOS Saipanloader V1.0.7
Built Mar 19 2009/15:54:12
watchdog_probe, 1132 bus/dev/fn = 0/248 ich = 2640
boot_drive = 80
start1 = 0768, start2 = 3840
Hit 'X' and 'A' to upgrade bootloader <- Hold ‘Shift key’ and hit ‘X’ and ‘A’ in sequence
Loader File Name:new/Loadssg500v107.d <- Bootloader filename signed with the new image key
Self IP Address :172.22.152.35 <- TFTP client IP address
TFTP IP Address :172.22.152.251 <- TFTP server IP address
IP MASK :255.255.255.0
Gateway IP Address :172.22.152.1
Saipan motherboard proto 3 or later detected
Probing...[Ethernet0/0 and Ethernet0/1]
Initiating hardware and waiting for link up ...
Initiating hardware and waiting for link up ...
self_ip = 172.22.152.35, tftp_server_ip = 172.22.152.251
ip = 172.22.152.35 mask = 255.255.255.0 gw = 172.22.152.1 svr = 172.22.152.251
network_ready = 1
new/Loadssg500v107.d
121078 bytes downloaded from tftp server
old img size = 121032, new img size = 121032, load = 121078, sig = 46
S
Image authenticated! <- Bootloader is authenticated using the new image key
mounting FAT12 partition
file /boot2 size was 121079, new size is 121078
getting sector information
boot1 size = 512
boot2 size = 512
boot1_sector = 807, boot2_sector = 1051
offset = 512
[1052][1053][1054][1055][1056][1057][1058][1059][1060][1061][1062][1063][1064][1065][1066][1067][1068][1069][1070][1071][1072][1073][1074][1075][1076][1077][1078][1079][1080][1081][1082][1083][1084][1085][1086][1087][1088][1089][1090][1091][1092][1093][1094][1095][1096][1097][1098][1099][1100][1101][1102][1103][1104][1105][1106][1107][1108][1109][1110][1111][1112][1113][1114][1115][1116][1117][1118][1119][1120][1121][1122][1123][1124][1125][1126][1127][1128][1129][1130][1131][1132][1133][1134][1135][1136][1137][1138][1139][1140][1141][1142][1143][1144][1145][1146][1147][1148][1149][1150][1151][1152][1153][1154][1155][1156][1157][1158][1159][1160][1161][1162][1163][1164][1165][1166][1167][1168][1169][1170][1171][1172][1173][1174][1175][1176][1177][1178][1179][1180][1181][1182][1183][1184][1185][1186][1187][1188][1189][1190][1191][1192][1193][1194][1195][1196][1197][1198][1199][1200][1201][1202][1203][1204][1205][1206][1207][1208][1209][1210][1211][1212][1213][1214][1215][1216][1217][1218][1219][1220][1221][1222][1223][1224][1225][1226][1227][1228][1229][1230][1231][1232][1233][1234][1235][1236][1237][1238][1239][1240][1241][1242][1243][1244][1245][1246][1247][1248][1249][1250][1251][1252][1253][1254][1255][1256][1257][1258][1259][1260][1261][1262][1263][1264][1265][1266][1267][1268][1269][1270][1271][1272][1273][1274][1275][1276][1277][1278][1279][1280][1281][1282][1283][1284][1285][1286][1287][1288][1289][1290]
write boot2's start sector back at sector 1051
write mbr back at sector 0
mounting FAT16 partition
file size = 112
size = 112, sizeof(nvram_rec) = 112
system rebooting... <- After successful bootloader installation, the device will automatically try to reboot
(snip)
********Invalid DSA signature <- But if the previously installed ScreenOS firmware is signed with the old image key, the new image key cannot authenticate the ScreenOS firmware, then the device prompt to you install a ScreenOS firmware signed with the new image key
********Bogus image - not authenticated
mounting FAT16 partition
file size = 112
Serial Number []: READ ONLYc) = 112
BOM Version Number []: READ ONLY
Self MAC Address [0000-0000-0000]: READ ONLYip = 1.1.1.1 svr = 1.1.1.2
self_ip_buf = 1.1.1.1, tftp_ip_buf = 1.1.1.2
Firmware File Name [old/ssg500.6.3.0r17.0]: new/ssg500.6.3.0r17.0 <- Type the ScreenOS firmware filename signed with the new image key
Self IP Address [1.1.1.1]: 172.22.152.35 <- TFTP client IP address
TFTP IP Address [1.1.1.2]: 172.22.152.251 <- TFTP server IP address
IP MASK [255.255.255.0]:
Gateway IP Address [172.22.152.251]:
Save loader config (112 bytes)... Done
Saipan motherboard proto 3 or later detected
Probing...[Ethernet0/0 and Ethernet0/1]
Initiating hardware and waiting for link up ...
self_ip = 172.22.152.35, tftp_server_ip = 172.22.152.251
ip = 172.22.152.35 mask = 255.255.255.0 gw = 172.22.152.251 svr = 172.22.152.251
network_ready = 1
new/ssg500.6.3.0r17.0
offset = 0, maxposition = 11627247
11627247 bytes downloaded from tftp server
hdr->magic_number = 81ba16ee, hdr->platform_type = 1700, hdr->cpu_type = 11
Image authenticated! ← ScreenOS is authenticated
Save to on-board flash disk? (y/[n]/m) No <- You should press ‘n’ key
Run downloaded system image? ([y]/n) Yes <- You should press ‘y’ key
(snip)
System change state to Active(1)
login:
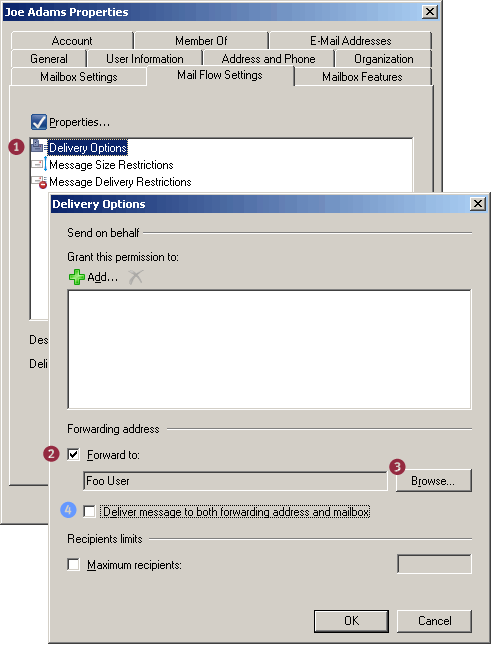
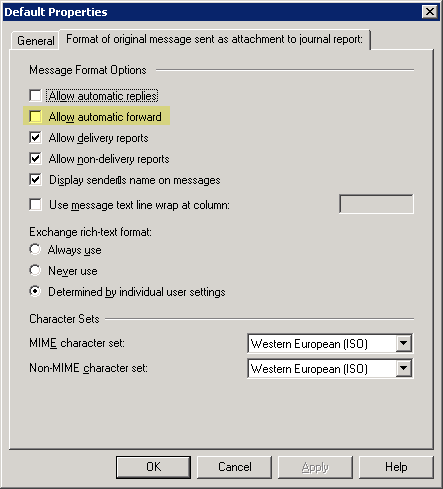
 Create a MailContact
Create a MailContact Forward mail for a recipient to the MailContact
Forward mail for a recipient to the MailContact